Overview of VLANs
Summary
This topic explain the purpose of VLANs in a switched networ. Start learning CCNA 200-301 for free right now!!
Table of Contents
VLAN Definitions
Of course organizing your network into smaller networks is not as simple as separating screws and putting them into jars. But it will make your network easier to manage. Virtual LANs (VLANs) provide segmentation and organizational flexibility in a switched network. A group of devices within a VLAN communicate as if each device was attached to the same cable. VLANs are based on logical connections, instead of physical connections.
As shown in the figure, VLANs in a switched network enable users in various departments (i.e., IT, HR, and Sales) to connect to the same network regardless of the physical switch being used or location in a campus LAN.
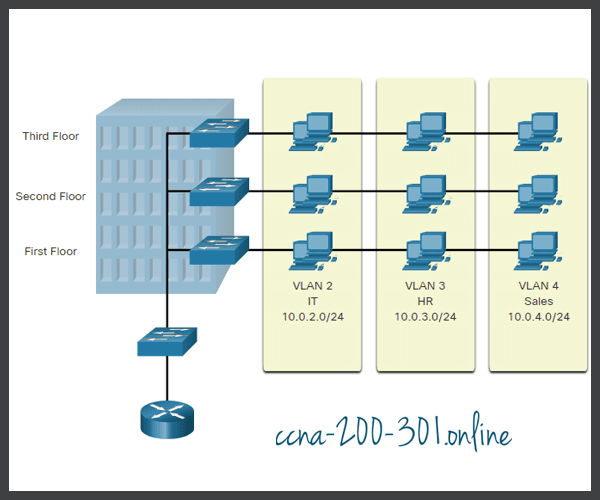
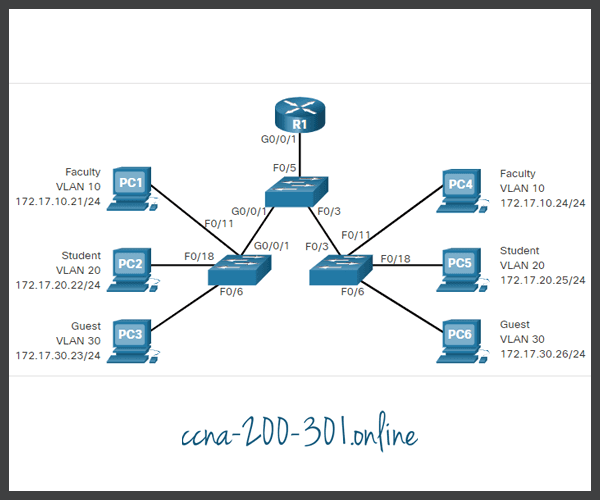
VLANs allow an administrator to segment networks based on factors such as function, team, or application, without regard for the physical location of the users or devices. Each VLAN is considered a separate logical network. Devices within a VLAN act as if they are in their own independent network, even if they share a common infrastructure with other VLANs. Any switch port can belong to a VLAN.
Unicast, broadcast, and multicast packets are forwarded and flooded only to end devices within the VLAN where the packets are sourced. Packets destined for devices that do not belong to the VLAN must be forwarded through a device that supports routing.
Multiple IP subnets can exist on a switched network, without the use of multiple VLANs. However, the devices will be in the same Layer 2 broadcast domain. This means that any Layer 2 broadcasts, such as an ARP request, will be received by all devices on the switched network, even by those not intended to receive the broadcast.
A VLAN creates a logical broadcast domain that can span multiple physical LAN segments. VLANs improve network performance by separating large broadcast domains into smaller ones. If a device in one VLAN sends a broadcast Ethernet frame, all devices in the VLAN receive the frame, but devices in other VLANs do not.
Using VLANs, network administrators can implement access and security policies according to specific groupings of users. Each switch port can be assigned to only one VLAN (except for a port connected to an IP phone or to another switch).
Benefits of a VLAN Design
Each VLAN in a switched network corresponds to an IP network. Therefore, VLAN design must take into consideration the implementation of a hierarchical network-addressing scheme. Hierarchical network addressing means that IP network numbers are applied to network segments or VLANs in a way that takes the network as a whole into consideration. Blocks of contiguous network addresses are reserved for and configured on devices in a specific area of the network, as shown in the figure.
The table lists the benefits of designing a network with VLANs.
| Benefit | Description |
|---|---|
| Smaller broadcast domains |
|
| Improved security |
|
| Improved IT efficiency |
|
| Reduced cost | VLANs reduce the need for expensive network upgrades and use the existing bandwidth and uplinks more efficiently, resulting in cost savings. |
| Better performance | Smaller broadcast domains reduce unnecessary traffic on the network and improve performance. |
| Simpler project and application management |
|
Types of VLANs
VLANs are used for different reasons in modern networks. Some VLAN types are defined by traffic classes. Other types of VLANs are defined by the specific function that they serve.
Click each VLAN type for more information.
Packet Tracer – Who Hears the Broadcast?
In this Packet Tracer activity, you will complete the following objectives:
- Part 1: Observe Broadcast Traffic in a VLAN Implementation
- Part 2: Complete Review Questions
Ready to go! Keep visiting our networking course blog, give Like to our fanpage; and you will find more tools and concepts that will make you a networking professional.