Configure Extended IPv4 ACLs
Summary
This topic configure extended IPv4 ACLs to filter traffic according to networking requirements. Start learning CCNA 200-301 for free right now!!
Table of Contents
Extended ACLs
In the previous topics, you learned about how to configure and modify standard ACLs, and how to secure VTY ports with a standard IPv4 ACL. Standard ACLs only filter on source address. When more precise traffic-filtering control is required, extended IPv4 ACLs can be created.
Extended ACLs are used more often than standard ACLs because they provide a greater degree of control. They can filter on source address, destination address, protocol (i.e., IP, TCP, UDP, ICMP), and port number. This provides a greater range of criteria on which to base the ACL. For example, one extended ACL can allow email traffic from a network to a specific destination while denying file transfers and web browsing.
Like standard ACLs, extended ACLs can be created as:
- Numbered Extended ACL – Created using the access-list access-list-number global configuration command.
- Named Extended ACL – Created using the ip access-list extended access-list-name.
Numbered Extended IPv4 ACL Syntax
The procedural steps for configuring extended ACLs are the same as for standard ACLs. The extended ACL is first configured, and then it is activated on an interface. However, the command syntax and parameters are more complex to support the additional features provided by extended ACLs.
To create a numbered extended ACL, use the following global configuration command:
Router(config)# access-list access-list-number {deny | permit | remark text}
protocol source source-wildcard [operator {port}] destination destination-wildcard [operator {port}] [established] [log]Use the no access-list access-list-number global configuration command to remove an extended ACL.
Although there are many keywords and parameters for extended ACLs, it is not necessary to use all of them when configuring an extended ACL. The table provides a detailed explanation of the syntax for an extended ACL.
| Parameter | Description |
|---|---|
access-list-number |
|
deny | This denies access if the condition is matched. |
permit | This permits access if the condition is matched. |
remark text |
|
protocol |
|
source |
|
source-wildcard | (Optional) A 32-bit wildcard mask that is applied to the source. |
destination |
|
destination-wildcard | (Optional) This is a 32-bit wildcard mask that is applied to the destination. |
operator |
|
port | (Optional) The decimal number or name of a TCP or UDP port. |
established |
|
log |
|
The command to apply an extended IPv4 ACL to an interface is the same as the command used for standard IPv4 ACLs.
Router(config-if)# ip access-group {access-list-number | access-list-name} {in | out}To remove an ACL from an interface, first enter the no ip access-group interface configuration command. To remove the ACL from the router, use the no access-list global configuration command.
Protocols and Ports
Protocols and Port Numbers Configuration Examples
Extended ACLs can filter on different port number and port name options. This example configures an extended ACL 100 to filter HTTP traffic. The first ACE uses the www port name. The second ACE uses the port number 80. Both ACEs achieve exactly the same result.
R1(config)# access-list 100 permit tcp any any eq www !or... R1(config)# access-list 100 permit tcp any any eq 80
Configuring the port number is required when there is not a specific protocol name listed such as SSH (port number 22) or an HTTPS (port number 443), as shown in the next example.
R1(config)# access-list 100 permit tcp any any eq 22 R1(config)# access-list 100 permit tcp any any eq 443 R1(config)#
Apply a Numbered Extended IPv4 ACL
The topology in the figure will be used to demonstrate configuring and applying numbered and named extended IPv4 ACLs to an interface. This first example shows a numbered extended IPv4 ACL implementation.

In this example, the ACL permits both HTTP and HTTPS traffic from the 192.168.10.0 network to go to any destination.
Extended ACLs can be applied in various locations. However, they are commonly applied close to the source. Therefore, ACL 110 was applied inbound on the R1 G0/0/0 interface.
R1(config)# access-list 110 permit tcp 192.168.10.0 0.0.0.255 any eq www R1(config)# access-list 110 permit tcp 192.168.10.0 0.0.0.255 any eq 443 R1(config)# interface g0/0/0 R1(config-if)# ip access-group 110 in R1(config-if)# exit R1(config)#
TCP Established Extended ACL
TCP can also perform basic stateful firewall services using the TCP established keyword. The keyword enables inside traffic to exit the inside private network and permits the returning reply traffic to enter the inside private network, as shown in the figure.

However, TCP traffic generated by an outside host and attempting to communicate with an inside host is denied.
The established keyword can be used to permit only the return HTTP traffic from requested websites, while denying all other traffic.
In the topology, the design for this example shows that ACL 110, which was previously configured, will filter traffic from the inside private network. ACL 120, using the established keyword, will filter traffic coming into the inside private network from the outside public network.
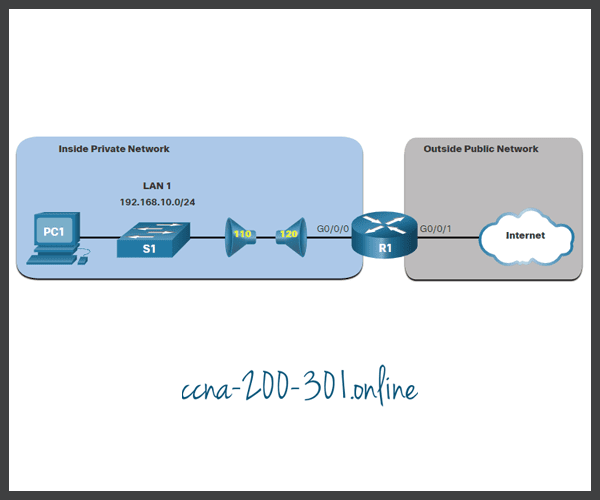
In the example, ACL 120 is configured to only permit returning web traffic to the inside hosts. The new ACL is then applied outbound on the R1 G0/0/0 interface. The show access-lists command displays both ACLs. Notice from the match statistics that inside hosts have been accessing the secure web resources from the internet.
R1(config)# access-list 120 permit tcp any 192.168.10.0 0.0.0.255 established
R1(config)# interface g0/0/0
R1(config-if)# ip access-group 120 out
R1(config-if)# end
R1# show access-lists
Extended IP access list 110
10 permit tcp 192.168.10.0 0.0.0.255 any eq www
20 permit tcp 192.168.10.0 0.0.0.255 any eq 443 (657 matches)
Extended IP access list 120
10 permit tcp any 192.168.10.0 0.0.0.255 established (1166 matches)
R1#Notice that the permit secure HTTPS counters (i.e., eq 443) in ACL 110 and the return established counters in ACL 120 have increased.
The established parameter allows only responses to traffic that originates from the 192.168.10.0/24 network to return to that network. Specifically, a match occurs if the returning TCP segment has the ACK or reset (RST) flag bits set. This indicates that the packet belongs to an existing connection. Without the established parameter in the ACL statement, clients could send traffic to a web server, and receive traffic returning from the web server. All traffic would be permitted.
Named Extended IPv4 ACL Syntax
Naming an ACL makes it easier to understand its function. To create a named extended ACL, use the following global configuration command:
Router(config)# ip access-list extendedaccess-list-name
This command enters the named extended configuration mode. Recall that ACL names are alphanumeric, case sensitive, and must be unique.
In the example, a named extended ACL called NO-FTP-ACCESS is created and the prompt changed to named extended ACL configuration mode. ACE statements are entered in the named extended ACL sub configuration mode.
R1(config)# ip access-list extended NO-FTP-ACCESS R1(config-ext-nacl)#
Named Extended IPv4 ACL Example
Named extended ACLs are created in essentially the same way that named standard ACLs are created.
The topology in the figure is used to demonstrate configuring and applying two named extended IPv4 ACLs to an interface:
- SURFING – This will permit inside HTTP and HTTPS traffic to exit to the internet.
- BROWSING – This will only permit returning web traffic to the inside hosts while all other traffic exiting the R1 G0/0/0 interface is implicitly denied.

The example shows the configuration for the inbound SURFING ACL and the outbound BROWSING ACL.
The SURFING ACL permits HTTP and HTTPS traffic from inside users to exit the G0/0/1 interface connected to the internet. Web traffic returning from the internet is permitted back into the inside private network by the BROWSING ACL.
The SURFING ACL is applied inbound and the BROWSING ACL applied outbound on the R1 G0/0/0 interface, as shown in the output.
Inside hosts have been accessing the secure web resources from the internet. The show access-lists command is used to verify the ACL statistics. Notice that the permit secure HTTPS counters (i.e., eq 443) in the SURFING ACL and the return established counters in the BROWSING ACL have increased.
R1(config)# ip access-list extended SURFING
R1(config-ext-nacl)# Remark Permits inside HTTP and HTTPS traffic
R1(config-ext-nacl)# permit tcp 192.168.10.0 0.0.0.255 any eq 80
R1(config-ext-nacl)# permit tcp 192.168.10.0 0.0.0.255 any eq 443
R1(config-ext-nacl)# exit
R1(config)#
R1(config)# ip access-list extended BROWSING
R1(config-ext-nacl)# Remark Only permit returning HTTP and HTTPS traffic
R1(config-ext-nacl)# permit tcp any 192.168.10.0 0.0.0.255 established
R1(config-ext-nacl)# exit
R1(config)# interface g0/0/0
R1(config-if)# ip access-group SURFING in
R1(config-if)# ip access-group BROWSING out
R1(config-if)# end
R1# show access-lists
Extended IP access list SURFING
10 permit tcp 192.168.10.0 0.0.0.255 any eq www
20 permit tcp 192.168.10.0 0.0.0.255 any eq 443 (124 matches)
Extended IP access list BROWSING
10 permit tcp any 192.168.10.0 0.0.0.255 established (369 matches)
R1#Edit Extended ACLs
Like standard ACLs, an extended ACL can be edited using a text editor when many changes are required. Otherwise, if the edit applies to one or two ACEs, then sequence numbers can be used.
For example, assume you have just entered the SURFING and BROWSING ACLs and wish to verify their configuration using the show access-lists command.
R1# show access-lists
Extended IP access list BROWSING
10 permit tcp any 192.168.10.0 0.0.0.255 established
Extended IP access list SURFING
10 permit tcp 19.168.10.0 0.0.0.255 any eq www
20 permit tcp 192.168.10.0 0.0.0.255 any eq 443
R1#You notice that the ACE sequence number 10 in the SURFING ACL has an incorrect source IP networks address.
To correct this error using sequence numbers, the original statement is removed with the no sequence_# command and the corrected statement is added replacing the original statement.
R1# configure terminal R1(config)# ip access-list extended SURFING R1(config-ext-nacl)# no 10 R1(config-ext-nacl)# 10 permit tcp 192.168.10.0 0.0.0.255 any eq www R1(config-ext-nacl)# end
The output verifies the configuration change using the show access-lists command.
R1# show access-lists
Extended IP access list BROWSING
10 permit tcp any 192.168.10.0 0.0.0.255 established
Extended IP access list SURFING
10 permit tcp 192.168.10.0 0.0.0.255 any eq www
20 permit tcp 192.168.10.0 0.0.0.255 any eq 443
R1#Another Named Extended IPv4 ACL Example
The figure shows another scenario for implementing a named extended IPv4 ACL. Assume that PC1 in the inside private network is permitted FTP, SSH, Telnet, DNS, HTTP, and HTTPS traffic. However, all other users in the inside private network should be denied access.
Two named extended ACLs will be created:
- PERMIT-PC1 – This will only permit PC1 TCP access to the internet and deny all other hosts in the private network.
- REPLY-PC1 – This will only permit specified returning TCP traffic to PC1 implicitly deny all other traffic.

The example shows the configuration for the inbound PERMIT-PC1 ACL and the outbound REPLY-PC1.
The PERMIT-PC1 ACL permits PC1 (i.e., 192.168.10.10) TCP access to the FTP (i.e., ports 20 and 21), SSH (22), Telnet (23), DNS (53), HTTP (80), and HTTPS (443) traffic. DNS (53) is permitted for both TCP and UDP.
The REPLY-PC1 ACL will permit return traffic to PC1.
There are many factors to consider when applying an ACL including:
- The device to apply it on
- The interface to apply it on
- The direction to apply it
Careful consideration must be taken to avoid undesired filtering results. The PERMIT-PC1 ACL is applied inbound and the REPLY-PC1 ACL applied outbound on the R1 G0/0/0 interface.
R1(config)# ip access-list extended PERMIT-PC1 R1(config-ext-nacl)# Remark Permit PC1 TCP access to internet R1(config-ext-nacl)# permit tcp host 192.168.10.10 any eq 20 R1(config-ext-nacl)# permit tcp host 192.168.10.10 any eq 21 R1(config-ext-nacl)# permit tcp host 192.168.10.10 any eq 22 R1(config-ext-nacl)# permit tcp host 192.168.10.10 any eq 23 R1(config-ext-nacl)# permit udp host 192.168.10.10 any eq 53 R1(config-ext-nacl)# permit tcp host 192.168.10.10 any eq 53 R1(config-ext-nacl)# permit tcp host 192.168.10.10 any eq 80 R1(config-ext-nacl)# permit tcp host 192.168.10.10 any eq 443 R1(config-ext-nacl)# deny ip 192.168.10.0 0.0.0.255 any R1(config-ext-nacl)# exit R1(config)# R1(config)# ip access-list extended REPLY-PC1 R1(config-ext-nacl)# Remark Only permit returning traffic to PC1 R1(config-ext-nacl)# permit tcp any host 192.168.10.10 established R1(config-ext-nacl)# exit R1(config)# interface g0/0/0 R1(config-if)# ip access-group PERMIT-PC1 in R1(config-if)# ip access-group REPLY-PC1 out R1(config-if)# end R1#
Verify Extended ACLs
After an ACL has been configured and applied to an interface, use Cisco IOS show commands to verify the configuration.
Packet Tracer – Configure Extended IPv4 ACLs – Scenario 1
In this Packet Tracer activity, you will complete the following objectives:
- Part 1: Configure, Apply, and Verify an Extended Numbered IPv4 ACL
- Part 2: Configure, Apply, and Verify an Extended Named IPv4 ACL
Packet Tracer – Configure Extended IPv4 ACLs – Scenario 2
In this Packet Tracer activity, you will complete the following objectives:
- Part 1: Configure a Named Extended IPv4 ACL
- Part 2: Apply and Verify the Extended IPv4 ACL
Ready to go! Keep visiting our networking course blog, give Like to our fanpage; and you will find more tools and concepts that will make you a networking professional.