VPN Technology
Summary
This topic describe benefits of VPN technology. Start learning CCNA 200-301 for free right now!!
Table of Contents
Virtual Private Networks
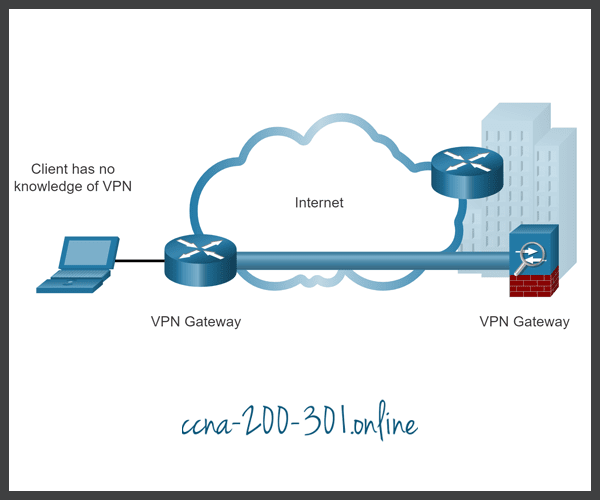
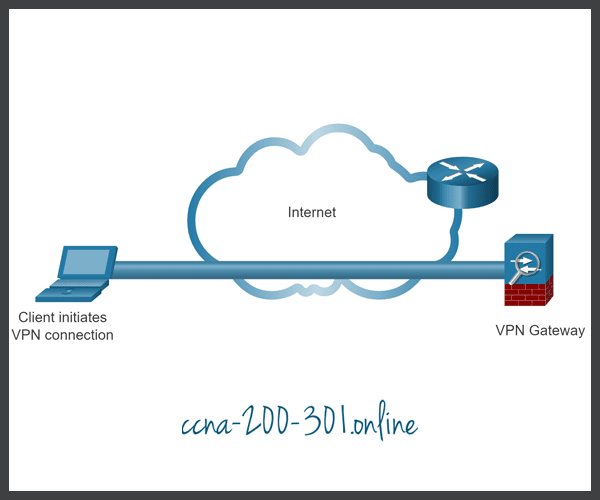
To secure network traffic between sites and users, organizations use virtual private networks (VPNs) to create end-to-end private network connections. A VPN is virtual in that it carries information within a private network, but that information is actually transported over a public network. A VPN is private in that the traffic is encrypted to keep the data confidential while it is transported across the public network.
The figure shows a collection of various types of VPNs managed by an enterprise’s main site. The tunnel enables remote sites and users to access main site’s network resources securely.

- A Cisco Adaptive Security Appliance (ASA) firewall helps organizations provide secure, high performance connectivity including VPNs and always-on access for remote branches and mobile users.
- SOHO stands for small office home office where a VPN-enabled router can provide VPN connectivity back to the corporate main site.
- Cisco AnyConnect is software that remote workers can use to establish client-based VPN connection with the main site.
The first types of VPNs were strictly IP tunnels that did not include authentication or encryption of the data. For example, Generic Routing Encapsulation (GRE) is a tunneling protocol developed by Cisco and which does not include encryption services. It is used to encapsulate IPv4 and IPv6 traffic inside an IP tunnel to create a virtual point-to-point link.
VPN Benefits
Modern VPNs now support encryption features, such as Internet Protocol Security (IPsec) and Secure Sockets Layer (SSL) VPNs to secure network traffic between sites.
Major benefits of VPNs are shown in the table.
| Benefit | Description |
|---|---|
| Cost Savings | With the advent of cost-effective, high-bandwidth technologies, organizations can use VPNs to reduce their connectivity costs while simultaneously increasing remote connection bandwidth. |
| Security | VPNs provide the highest level of security available, by using advanced encryption and authentication protocols that protect data from unauthorized access. |
| Scalability | VPNs allow organizations to use the internet, making it easy to add new users without adding significant infrastructure. |
| Compatibility | VPNs can be implemented across a wide variety of WAN link options including all the popular broadband technologies. Remote workers can take advantage of these high-speed connections to gain secure access to their corporate networks. |
Site-to-Site and Remote-Access VPNs
VPNs are commonly deployed in one of the following configurations: site-to-site or remote-access.
Enterprise and Service Provider VPNs
There are many options available to secure enterprise traffic. These solutions vary depending on who is managing the VPN.
VPNs can be managed and deployed as:
- Enterprise VPNs – Enterprise-managed VPNs are a common solution for securing enterprise traffic across the internet. Site-to-site and remote access VPNs are created and managed by the enterprise using both IPsec and SSL VPNs.
- Service Provider VPNs – Service provider-managed VPNs are created and managed over the provider network. The provider uses Multiprotocol Label Switching (MPLS) at Layer 2 or Layer 3 to create secure channels between an enterprise’s sites. MPLS is a routing technology the provider uses to create virtual paths between sites. This effectively segregates the traffic from other customer traffic. Other legacy solutions include Frame Relay and Asynchronous Transfer Mode (ATM) VPNs.
The figure lists the different types of enterprise-managed and service provider-managed VPN deployments that will be discussed in more detail in this module.

Ready to go! Keep visiting our networking course blog, give Like to our fanpage; and you will find more tools and concepts that will make you a networking professional.