Troubleshooting IP Connectivity
Summary
This topic troubleshoot a network using the layered model. Start learning CCNA 200-301 for free right now!!
Table of Contents
Components of Troubleshooting End-to-End Connectivity
This topic presents a single topology and the tools to diagnose, and in some cases solve, an end-to-end connectivity problem. Diagnosing and solving problems is an essential skill for network administrators. There is no single recipe for troubleshooting, and a problem can be diagnosed in many ways. However, by employing a structured approach to the troubleshooting process, an administrator can reduce the time it takes to diagnose and solve a problem.
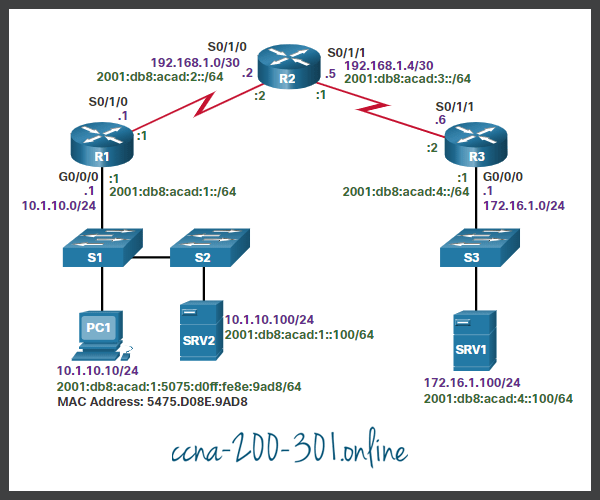
Throughout this topic, the following scenario is used. The client host PC1 is unable to access applications on Server SRV1 or Server SRV2. The figure shows the topology of this network. PC1 uses SLAAC with EUI-64 to create its IPv6 global unicast address. EUI-64 creates the Interface ID using the Ethernet MAC address, inserting FFFE in the middle, and flipping the seventh bit.
When there is no end-to-end connectivity, and the administrator chooses to troubleshoot with a bottom-up approach, the following are common steps the administrator can take:
- Step 1. Check physical connectivity at the point where network communication stops. This includes cables and hardware. The problem might be with a faulty cable or interface, or involve misconfigured or faulty hardware.
- Step 2. Check for duplex mismatches.
- Step 3. Check data link and network layer addressing on the local network. This includes IPv4 ARP tables, IPv6 neighbor tables, MAC address tables, and VLAN assignments.
- Step 4. Verify that the default gateway is correct.
- Step 5. Ensure that devices are determining the correct path from the source to the destination. Manipulate the routing information if necessary.
- Step 6. Verify the transport layer is functioning properly. Telnet can also be used to test transport layer connections from the command line.
- Step 7. Verify that there are no ACLs blocking traffic.
- Step 8. Ensure that DNS settings are correct. There should be a DNS server that is accessible.
The outcome of this process is operational, end-to-end connectivity. If all the steps have been performed without any resolution, the network administrator may either want to repeat the previous steps or escalate the problem to a senior administrator.
End-to-End Connectivity Problem Initiates Troubleshooting
Usually what initiates a troubleshooting effort is the discovery that there is a problem with end-to-end connectivity. Two of the most common utilities used to verify a problem with end-to-end connectivity are ping and traceroute, as shown in the figure.

Step 1 – Verify the Physical Layer
All network devices are specialized computer systems. At a minimum, these devices consist of a CPU, RAM, and storage space, allowing the device to boot and run the operating system and interfaces. This allows for the reception and transmission of network traffic. When a network administrator determines that a problem exists on a given device, and that problem might be hardware-related, it is worthwhile to verify the operation of these generic components. The most commonly used Cisco IOS commands for this purpose are show processes cpu, show memory, and show interfaces. This topic discusses the show interfaces command.
When troubleshooting performance-related issues and hardware is suspected to be at fault, the show interfaces command can be used to verify the interfaces through which the traffic passes.
Refer to the command output of the show interfaces command.
R1# show interfaces GigabitEthernet 0/0/0 GigabitEthernet0/0/0 is up, line protocol is up Hardware is CN Gigabit Ethernet, address is d48c.b5ce.a0c0(bia d48c.b5ce.a0c0) Internet address is 10.1.10.1/24 (Output omitted) Input queue: 0/75/0/0 (size/max/drops/flushes); Total output drops: 0 Queueing strategy: fifo Output queue: 0/40 (size/max) 5 minute input rate 0 bits/sec, 0 packets/sec 5 minute output rate 0 bits/sec, 0 packets/sec 85 packets input, 7711 bytes, 0 no buffer Received 25 broadcasts (0 IP multicasts) 0 runts, 0 giants, 0 throttles 0 input errors, 0 CRC, 0 frame, 0 overrun, 0 ignored 0 watchdog, 5 multicast, 0 pause input 10112 packets output, 922864 bytes, 0 underruns 0 output errors, 0 collisions, l interface resets 11 unknown protocol drops 0 babbles, 0 late collision, 0 deferred 0 lost carrier, 0 no carrier, 0 pause output 0 output buffer failures, 0 output buffers swapped out R1#
Step 2 – Check for Duplex Mismatches
Another common cause for interface errors is a mismatched duplex mode between two ends of an Ethernet link. In many Ethernet-based networks, point-to-point connections are now the norm, and the use of hubs and the associated half-duplex operation is becoming less common. This means that most Ethernet links today operate in full-duplex mode, and while collisions were normal for an Ethernet link, collisions today often indicate that duplex negotiation has failed, or the link is not operating in the correct duplex mode.
The IEEE 802.3ab Gigabit Ethernet standard mandates the use of autonegotiation for speed and duplex. In addition, although it is not strictly mandatory, practically all Fast Ethernet NICs also use autonegotiation by default. The use of autonegotiation for speed and duplex is the current recommended practice.
However, if duplex negotiation fails for some reason, it might be necessary to set the speed and duplex manually on both ends. Typically, this would mean setting the duplex mode to full-duplex on both ends of the connection. If this does not work, running half-duplex on both ends is preferred over a duplex mismatch.
Duplex configuration guidelines include the following:
- Autonegotiation of speed and duplex is recommended.
- If autonegotiation fails, manually set the speed and duplex on interconnecting ends.
- Point-to-point Ethernet links should always run in full-duplex mode.
- Half-duplex is uncommon and typically encountered only when legacy hubs are used.
Troubleshooting Example
In the previous scenario, the network administrator needed to add additional users to the network. To incorporate these new users, the network administrator installed a second switch and connected it to the first. Soon after S2 was added to the network, users on both switches began experiencing significant performance problems connecting with devices on the other switch, as shown in the figure.
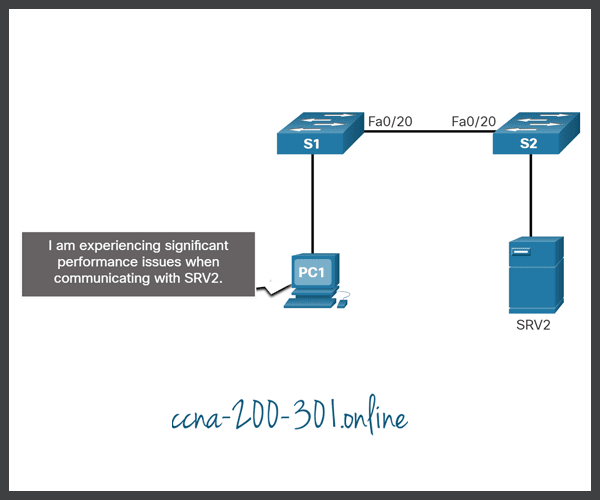
The network administrator notices a console message on switch S2:
*Mar 1 00:45:08.756: %CDP-4-DUPLEX_MISMATCH: duplex mismatch discovered on FastEthernet0/20 (not half duplex), with Switch FastEthernet0/20 (half duplex).
Using the show interfaces fa 0/20 command, the network administrator examines the interface on S1 that is used to connect to S2 and notices it is set to full-duplex, as shown the command output.
S1# show interface fa 0/20 FastEthernet0/20 is up, line protocol is up (connected) Hardware is Fast Ethernet, address is 0cd9.96e8.8a01 (bia 0cd9.96e8.8a01) MTU 1500 bytes, BW 10000 Kbit/sec, DLY 1000 usec, reliability 255/255, txload 1/255, rxload 1/255 Encapsulation ARPA, loopback not set Keepalive set (10 sec) Full-duplex, Auto-speed, media type is 10/100BaseTX (Output omitted) S1#
The network administrator now examines the other side of the connection, the port on S2. The command out shows that this side of the connection has been configured for half-duplex.
S2# show interface fa 0/20 FastEthernet0/20 is up, line protocol is up (connected) Hardware is Fast Ethernet, address is 0cd9.96d2.4001 (bia 0cd9.96d2.4001) MTU 1500 bytes, BW 100000 Kbit/sec, DLY 100 usec, reliability 255/255, txload 1/255, rxload 1/255 Encapsulation ARPA, loopback not set Keepalive set (10 sec) Half-duplex, Auto-speed, media type is 10/100BaseTX (Output omitted) S2(config)# interface fa 0/20 S2(config-if)# duplex auto S2(config-if)#
The network administrator corrects the setting to duplex auto to automatically negotiate the duplex. Because the port on S1 is set to full-duplex, S2 also uses full-duplex.
The users report that there are no longer any performance problems.
Step 3 – Verify Addressing on the Local Network
When troubleshooting end-to-end connectivity, it is useful to verify mappings between destination IP addresses and Layer 2 Ethernet addresses on individual segments. In IPv4, this functionality is provided by ARP. In IPv6, the ARP functionality is replaced by the neighbor discovery process and ICMPv6. The neighbor table caches IPv6 addresses and their resolved Ethernet physical (MAC) addresses.
Troubleshoot VLAN Assignment Example
Another issue to consider when troubleshooting end-to-end connectivity is VLAN assignment. In the switched network, each port in a switch belongs to a VLAN. Each VLAN is considered a separate logical network, and packets destined for stations that do not belong to the VLAN must be forwarded through a device that supports routing. If a host in one VLAN sends a broadcast Ethernet frame, such as an ARP request, all hosts in the same VLAN receive the frame; hosts in other VLANs do not. Even if two hosts are in the same IP network, they will not be able to communicate if they are connected to ports assigned to two separate VLANs. Additionally, if the VLAN to which the port belongs is deleted, the port becomes inactive. All hosts attached to ports belonging to the VLAN that was deleted are unable to communicate with the rest of the network. Commands such as show vlan can be used to validate VLAN assignments on a switch.
Assume for example, that in an effort to improve the wire management in the wiring closet, your company has reorganized the cables connecting to switch S1. Almost immediately afterward, users started calling the support desk stating that they could no longer reach devices outside their own network.
Step 4 – Verify Default Gateway
If there is no detailed route on the router, or if the host is configured with the wrong default gateway, then communication between two endpoints in different networks does not work.
The figure illustrates how PC1 uses R1 as its default gateway. Similarly, R1 uses R2 as its default gateway or gateway of last resort. If a host needs access to resources beyond the local network, the default gateway must be configured. The default gateway is the first router on the path to destinations beyond the local network.

Troubleshooting IPv4 Default Gateway Example
In this example, R1 has the correct default gateway, which is the IPv4 address of R2. However, PC1 has the wrong default gateway. PC1 should have the default gateway of R1 10.1.10.1. This must be configured manually if the IPv4 addressing information was manually configured on PC1. If the IPv4 addressing information was obtained automatically from a DHCPv4 server, then the configuration on the DHCP server must be examined. A configuration problem on a DHCP server usually affects multiple clients.
Troubleshoot IPv6 Default Gateway Example
In IPv6, the default gateway can be configured manually, using stateless autoconfiguration (SLAAC), or by using DHCPv6. With SLAAC, the default gateway is advertised by the router to hosts using ICMPv6 Router Advertisement (RA) messages. The default gateway in the RA message is the link-local IPv6 address of a router interface. If the default gateway is configured manually on the host, which is very unlikely, the default gateway can be set to either the global IPv6 address, or to the link-local IPv6 address.
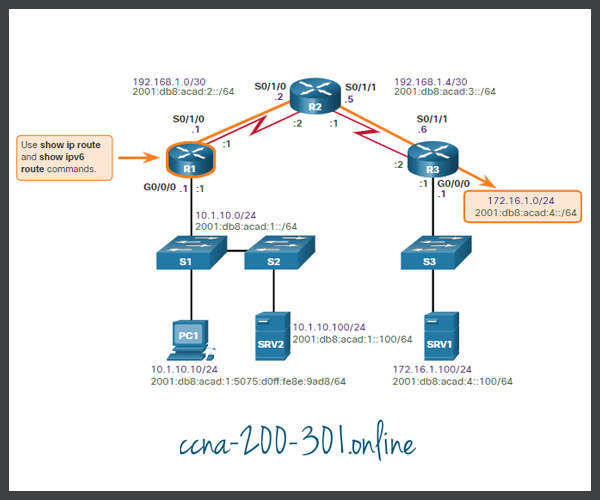
Step 5 – Verify Correct Path
When troubleshooting, it is often necessary to verify the path to the destination network. The figure shows the reference topology indicating the intended path for packets from PC1 to SRV1.
The IPv4 and IPv6 routing tables can be populated by the following methods:
- Directly connected networks
- Local host or local routes
- Static routes
- Dynamic routes
- Default routes
The process of forwarding IPv4 and IPv6 packets is based on the longest bit match or longest prefix match. The routing table process will attempt to forward the packet using an entry in the routing table with the greatest number of leftmost matching bits. The number of matching bits is indicated by the prefix length of the route.
The figure describes the process for both the IPv4 and IPv6 routing tables.
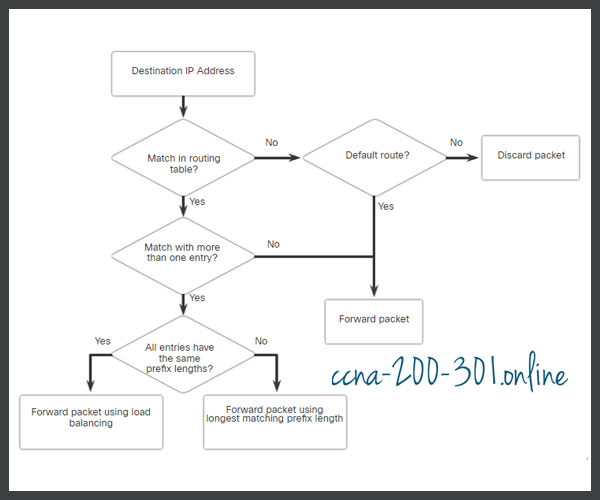
Examine the following scenarios based on the flow chart above. If the destination address in a packet:
- Does not match an entry in the routing table, then the default route is used. If there is not a default route that is configured, the packet is discarded.
- Matches a single entry in the routing table, then the packet is forwarded through the interface that is defined in this route.
- Matches more than one entry in the routing table and the routing entries have the same prefix length, then the packets for this destination can be distributed among the routes that are defined in the routing table.
- Matches more than one entry in the routing table and the routing entries have different prefix lengths, then the packets for this destination are forwarded out of the interface that is associated with the route that has the longer prefix match.
Troubleshooting Example
Devices are unable to connect to the server SRV1 at 172.16.1.100. Using the show ip route command, the administrator should check to see if a routing entry exists to network 172.16.1.0/24. If the routing table does not have a specific route to the SRV1 network, the network administrator must then check for the existence of a default or summary route entry in the direction of the 172.16.1.0/24 network. If none exists, then the problem may be with routing and the administrator must verify that the network is included within the dynamic routing protocol configuration or add a static route.
Step 6 – Verify the Transport Layer
If the network layer appears to be functioning as expected, but users are still unable to access resources, then the network administrator must begin troubleshooting the upper layers. Two of the most common issues that affect transport layer connectivity include ACL configurations and NAT configurations. A common tool for testing transport layer functionality is the Telnet utility.
Caution: While Telnet can be used to test the transport layer, for security reasons, SSH should be used to remotely manage and configure devices.
Troubleshooting Example
A network administrator is troubleshooting a problem where they cannot connect to a router using HTTP. The administrator pings R2 as shown in the command output.
R1# ping 2001:db8:acad:2::2 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 2001:DB8:ACAD:2::2, timeout is 2 seconds: !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 2/2/3 ms R1#
R2 responds and confirms that the network layer, and all layers below the network layer are operational. The administrator knows the issue is with Layer 4 or up and must start troubleshooting those layers.
Next, the administrator verifies that they can Telnet to R2 as shown in the command output.
R1# telnet 2001:db8:acad:2::2 Trying 2001:DB8:ACAD:2::2 ... Open User Access Verification Password: R2> exit [Connection to 2001:db8:acad:2::2 closed by foreign host] R1#
The administrator has confirmed that Telnet services is running on R2. Although the Telnet server application runs on its own well-known port number 23 and Telnet clients connect to this port by default, a different port number can be specified on the client to connect to any TCP port that must be tested. Using a different port other than TCP port 23 indicates whether the connection is accepted (as indicated by the word “Open” in the output), refused, or times out. From any of those responses, further conclusions can be made concerning the connectivity. Certain applications, if they use an ASCII-based session protocol, might even display an application banner, it may be possible to trigger some responses from the server by typing in certain keywords, such as with SMTP, FTP, and HTTP.
For example, the administrator attempts to Telnet to R2 using port 80.
R1# telnet 2001:db8:acad:2::2 80 Trying 2001:DB8:ACAD:2::2, 80 ... Open ^C HTTP/1.1 400 Bad Request Date: Mon, 04 Nov 2019 12:34:23 GMT Server: cisco-IOS Accept-Ranges: none 400 Bad Request [Connection to 2001:db8:acad:2::2 closed by foreign host] R1#
The output verifies a successful transport layer connection, but R2 is refusing the connection using port 80.
Step 7 – Verify ACLs
On routers, there may be ACLs that prohibit protocols from passing through the interface in the inbound or outbound direction.
Use the show ip access-lists command to display the contents of all IPv4 ACLs and the show ipv6 access-list command to display the contents of all IPv6 ACLs configured on a router. The specific ACL can be displayed by entering the ACL name or number as an option for this command. The show ip interfaces and show ipv6 interfaces commands display IPv4 and IPv6 interface information that indicates whether any IP ACLs are set on the interface.
Troubleshooting Example
To prevent spoofing attacks, the network administrator decided to implement an ACL that is preventing devices with a source network address of 172.16.1.0/24 from entering the inbound S0/0/1 interface on R3, as shown in the figure. All other IP traffic should be allowed.
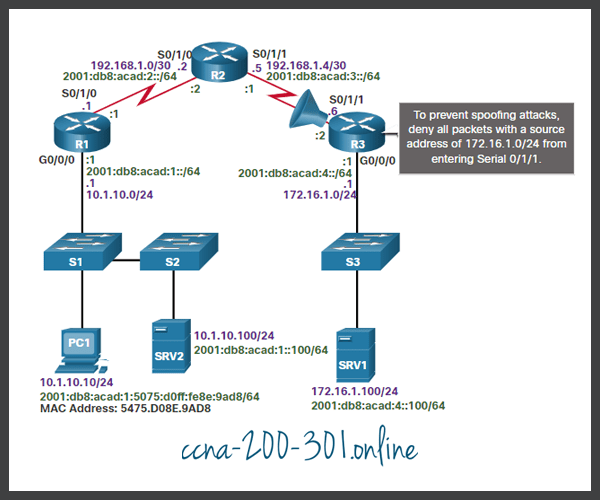
However, shortly after implementing the ACL, users on the 10.1.10.0/24 network were unable to connect to devices on the 172.16.1.0/24 network, including SRV1.
Step 8 – Verify DNS
The DNS protocol controls the DNS, a distributed database with which you can map hostnames to IP addresses. When you configure DNS on the device, you can substitute the hostname for the IP address with all IP commands, such as ping or telnet.
To display the DNS configuration information on the switch or router, use the show running-config command. When there is no DNS server installed, it is possible to enter names to IP mappings directly into the switch or router configuration. Use the ip host command to enter a name to be used instead of the IPv4 address of the switch or router, as shown in the command output.
R1(config)# ip host ipv4-server 172.16.1.100 R1(config)# exit R1#
Now the assigned name can be used instead of using the IP address, as shown in the command output.
R1# ping ipv4-server Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 172.16.1.100, timeout is 2 seconds: !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 4/5/7 ms R1#
To display the name-to-IP-address mapping information on a Windows-based PC, use the nslookup command.
Packet Tracer – Troubleshoot Enterprise Networks
This activity uses a variety of technologies you have encountered during your CCNA studies, including routing, port security, EtherChannel, DHCP, and NAT. Your task is to review the requirements, isolate and resolve any issues, and then document the steps you took to verify the requirements.
Ready to go! Keep visiting our networking course blog, give Like to our fanpage; and you will find more tools and concepts that will make you a networking professional.





