Cryptography
Summary
This topic describe common cryptographic processes used to protect data in transit. Start learning CCNA 200-301 for free right now!!
Table of Contents
Video – Cryptography
Early in the previous topic, cryptography is mentioned as part of the CIA information security triad. In this topic you will get a deeper dive into the many types of cryptography and how they are used to secure the network.
Click Play in the figure to view a video about cryptography.
Securing Communications
Organizations must provide support to secure the data as it travels across links. This may include internal traffic, but it is even more important to protect the data that travels outside of the organization to branch sites, telecommuter sites, and partner sites.
These are the four elements of secure communications:
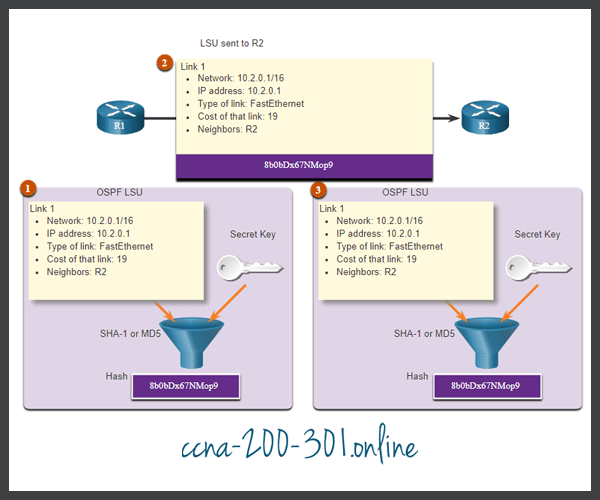
- Data Integrity – Guarantees that the message was not altered. Any changes to data in transit will be detected. Integrity is ensured by implementing either Message Digest version 5 (MD5) or Secure Hash Algorithm (SHA) hash-generating algorithms.
- Origin Authentication – Guarantees that the message is not a forgery and does actually come from whom it states. Many modern networks ensure authentication with protocols, such as hash message authentication code (HMAC).
- Data Confidentiality – Guarantees that only authorized users can read the message. If the message is intercepted, it cannot be deciphered within a reasonable amount of time. Data confidentiality is implemented using symmetric and asymmetric encryption algorithms.
- Data Non-Repudiation – Guarantees that the sender cannot repudiate, or refute, the validity of a message sent. Nonrepudiation relies on the fact that only the sender has the unique characteristics or signature for how that message is treated.
Cryptography can be used almost anywhere that there is data communication. In fact, the trend is toward all communication being encrypted.
Data Integrity
Hash functions are used to ensure the integrity of a message. They guarantee that message data has not changed accidentally or intentionally.
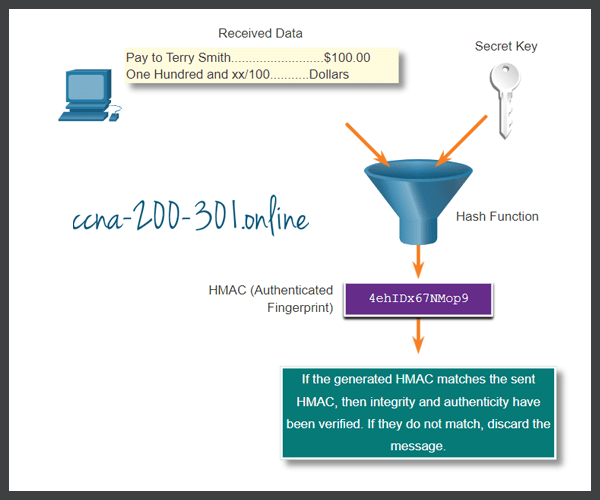
In the figure, the sender is sending a $100 money transfer to Alex.
Hash Algorithms
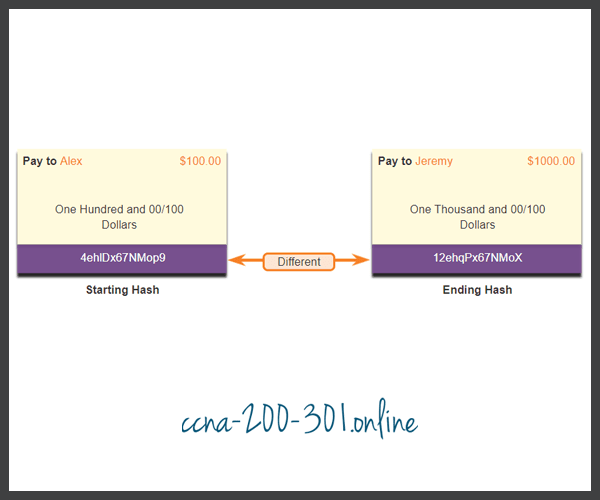
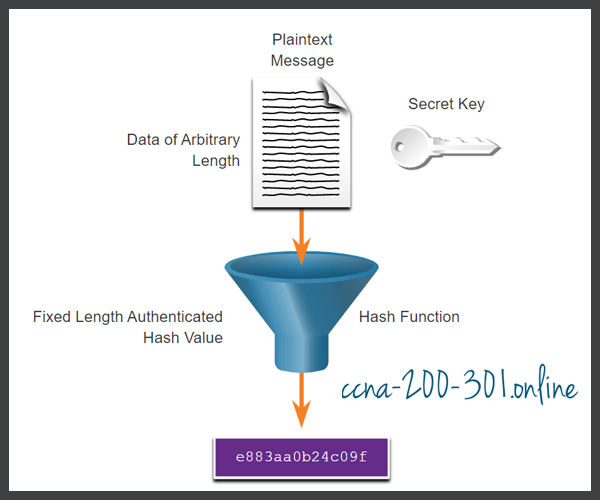
The sender wants to ensure that the message is not altered on its way to the receiver.
- The sending device inputs the message into a hashing algorithm and computes its fixed-length hash of 4ehiDx67NMop9.
- This hash is then attached to the message and sent to the receiver. Both the message and the hash are in plaintext.
- The receiving device removes the hash from the message and inputs the message into the same hashing algorithm. If the computed hash is equal to the one that is attached to the message, the message has not been altered during transit. If the hashes are not equal, as shown in the figure, then the integrity of the message can no longer be trusted.
Hash Functions
There are three well-known hash functions.
MD5 with 128-bit Digest
MD5 is a one-way function that produces a 128-bit hashed message, as shown in the figure. MD5 is a legacy algorithm that should only be used when no better alternatives are available. Use SHA-2 instead.
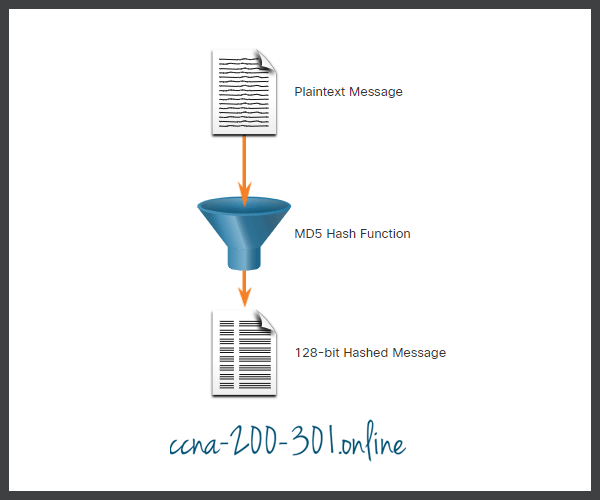
In the figure, a plaintext message is passed through an MD5 hash function. The result is a 128-bit hashed message.
SHA Hashing Algorithm
SHA-1 is very similar to the MD5 hash functions, as shown in the figure. Several versions exist. SHA-1 creates a 160-bit hashed message and is slightly slower than MD5. SHA-1 has known flaws and is a legacy algorithm. Use SHA-2 when possible.

In the figure, a plaintext message is passed through a SHA hash function. The result is a hashed message.
SHA-2
This includes SHA-224 (224 bit), SHA-256 (256 bit), SHA-384 (384 bit), and SHA-512 (512 bit). SHA-256, SHA-384, and SHA-512 are next-generation algorithms and should be used whenever possible.
While hashing can be used to detect accidental changes, it cannot be used to guard against deliberate changes. There is no unique identifying information from the sender in the hashing procedure. This means that anyone can compute a hash for any data, if they have the correct hash function.
For example, when the message traverses the network, a potential threat actor could intercept the message, change it, recalculate the hash, and append it to the message. The receiving device will only validate against whatever hash is appended.
Therefore, hashing is vulnerable to man-in-the-middle attacks and does not provide security to transmitted data. To provide integrity and origin authentication, something more is required.
Origin Authentication
To add authentication to integrity assurance, use a keyed-hash message authentication code (HMAC). HMAC uses an additional secret key as input to the hash function.
Data Confidentiality
There are two classes of encryption used to provide data confidentiality. These two classes differ in how they use keys.
Symmetric encryption algorithms such as (DES), 3DES, and Advanced Encryption Standard (AES) are based on the premise that each communicating party knows the pre-shared key. Data confidentiality can also be ensured using asymmetric algorithms, including Rivest, Shamir, and Adleman (RSA) and the public key infrastructure (PKI).
The figure highlights some differences between each encryption algorithm method.

Symmetric Encryption
Symmetric algorithms use the same pre-shared key to encrypt and decrypt data. A pre-shared key, also called a secret key, is known by the sender and receiver before any encrypted communications can take place.
To help illustrate how symmetric encryption works, consider an example where Alice and Bob live in different locations and want to exchange secret messages with one another through the mail system. In this example, Alice wants to send a secret message to Bob.
In the figure, Alice and Bob have identical keys to a single padlock. These keys were exchanged prior to sending any secret messages. Alice writes a secret message and puts it in a small box that she locks using the padlock with her key. She mails the box to Bob. The message is safely locked inside the box as the box makes its way through the post office system. When Bob receives the box, he uses his key to unlock the padlock and retrieve the message. Bob can use the same box and padlock to send a secret reply to Alice.
Symmetric Encryption Example
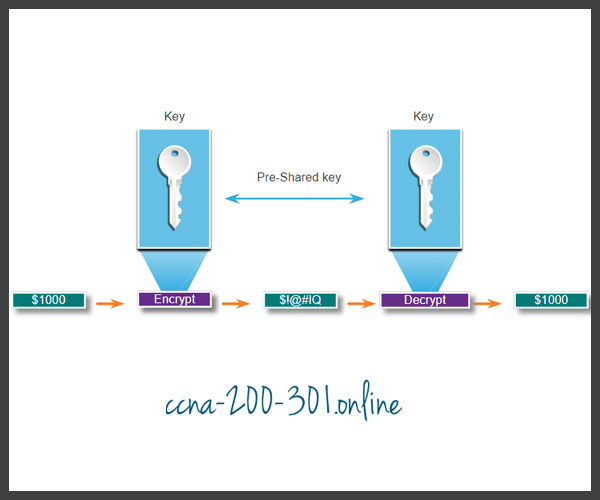
Today, symmetric encryption algorithms are commonly used with VPN traffic. This is because symmetric algorithms use less CPU resources than asymmetric encryption algorithms. Encryption and decryption of data is fast when using a VPN. When using symmetric encryption algorithms, like any other type of encryption, the longer the key, the longer it will take for someone to discover the key. Most encryption keys are between 112 and 256 bits. To ensure that the encryption is safe, use a minimum key length of 128 bits. Use a longer key for more secure communications.
Well-known symmetric encryption algorithms are described in the table.
| Symmetric Encryption Algorithms | Description |
|---|---|
| Data Encryption Standard (DES) | This is a legacy symmetric encryption algorithm. It can be used in stream cipher mode but usually operates in block mode by encrypting data in 64-bit block size. A stream cipher encrypts one byte or one bit at a time. |
| 3DES (Triple DES) | This is a newer version of DES, but it repeats the DES algorithm process three times. The basic algorithm has been well tested in the field for more than 35 years. It is considered very trustworthy when implemented using very short key lifetimes. |
| Advanced Encryption Standard (AES) | AES is a secure and more efficient algorithm than 3DES. It is a popular and recommended symmetric encryption algorithm. It offers nine combinations of key and block length by using a variable key length of 128-, 192-, or 256-bit key to encrypt data blocks that are 128, 192, or 256 bits long. |
| Software-Optimized Encryption Algorithm (SEAL) | SEAL is a faster alternative symmetric encryption algorithm to DES, 3DES, and AES. It uses a 160-bit encryption key and has a lower impact on the CPU compared to other software-based algorithms. |
| Rivest ciphers (RC) series algorithms | This algorithm was developed by Ron Rivest. Several variations have been developed, but RC4 is the most prevalent in use. RC4 is a stream cipher and is used to secure web traffic in SSL and TLS. |
Asymmetric Encryption
Asymmetric algorithms, also called public-key algorithms, are designed so that the key that is used for encryption is different from the key that is used for decryption, as shown in the figure. The decryption key cannot, in any reasonable amount of time, be calculated from the encryption key and vice versa.
Asymmetric algorithms use a public key and a private key. Both keys are capable of the encryption process, but the complementary paired key is required for decryption. The process is also reversible. Data encrypted with the public key requires the private key to decrypt. Asymmetric algorithms achieve confidentiality, authentication, and integrity by using this process.
Asymmetric Encryption Example

Because neither party has a shared secret, very long key lengths must be used. Asymmetric encryption can use key lengths between 512 to 4,096 bits. Key lengths greater than or equal to 1,024 bits can be trusted while shorter key lengths are considered unreliable.
Examples of protocols that use asymmetric key algorithms include:
- Internet Key Exchange (IKE) – This is a fundamental component of IPsec VPNs.
- Secure Socket Layer (SSL) – This is now implemented as IETF standard Transport Layer Security (TLS).
- Secure Shell (SSH) – This protocol provides a secure remote access connection to network devices.
- Pretty Good Privacy (PGP) – This computer program provides cryptographic privacy and authentication. It is often used to increase the security of email communications.
Asymmetric algorithms are substantially slower than symmetric algorithms. Their design is based on computational problems, such as factoring extremely large numbers or computing discrete logarithms of extremely large numbers.
Because they are slow, asymmetric algorithms are typically used in low-volume cryptographic mechanisms, such as digital signatures and key exchange. However, the key management of asymmetric algorithms tends to be simpler than symmetric algorithms, because usually one of the two encryption or decryption keys can be made public.
Common examples of asymmetric encryption algorithms are described in the table.
| Asymmetric Encryption Algorithm | Key Length | Description |
|---|---|---|
| Diffie-Hellman (DH) | 512, 1024, 2048, 3072, 4096 | The Diffie-Hellman algorithm allows two parties to agree on a key that they can use to encrypt messages they want to send to each other. The security of this algorithm depends on the assumption that it is easy to raise a number to a certain power, but difficult to compute which power was used given the number and the outcome. |
| Digital Signature Standard (DSS) and Digital Signature Algorithm (DSA) | 512 – 1024 | DSS specifies DSA as the algorithm for digital signatures. DSA is a public key algorithm based on the ElGamal signature scheme. Signature creation speed is similar to RSA, but is 10 to 40 times slower for verification. |
| Rivest, Shamir, and Adleman encryption algorithms (RSA) | 512 to 2048 | RSA is for public-key cryptography that is based on the current difficulty of factoring very large numbers. It is the first algorithm known to be suitable for signing as well as encryption. It is widely used in electronic commerce protocols and is believed to be secure given sufficiently long keys and the use of up-to-date implementations. |
| EIGamal | 512 – 1024 | An asymmetric key encryption algorithm for public-key cryptography which is based on the Diffie-Hellman key agreement. A disadvantage of the ElGamal system is that the encrypted message becomes very big, about twice the size of the original message and for this reason it is only used for small messages such as secret keys. |
| Elliptical curve techniques | 160 | Elliptic curve cryptography can be used to adapt many cryptographic algorithms, such as Diffie-Hellman or ElGamal. The main advantage of elliptic curve cryptography is that the keys can be much smaller. |
Diffie-Hellman
Diffie-Hellman (DH) is an asymmetric mathematical algorithm where two computers generate an identical shared secret key without having communicated before. The new shared key is never actually exchanged between the sender and receiver. However, because both parties know it, the key can be used by an encryption algorithm to encrypt traffic between the two systems.
Here are three examples of instances when DH is commonly used:
- Data is exchanged using an IPsec VPN.
- Data is encrypted on the internet using either SSL or TLS.
- SSH data is exchanged.
To help illustrate how DH operates, refer to the figure.
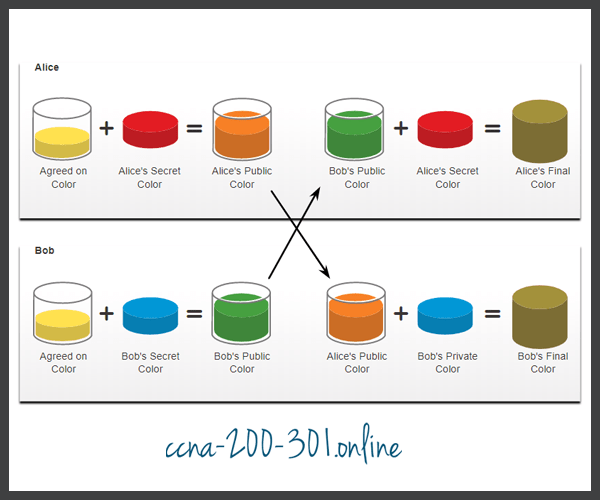
The colors in the figure will be used instead of complex long numbers to simplify the DH key agreement process. The DH key exchange begins with Alice and Bob agreeing on an arbitrary common color that does not need to be kept secret. The agreed-on color in our example is yellow.
Next, Alice and Bob will each select a secret color. Alice chose red while Bob chose blue. These secret colors will never be shared with anyone. The secret color represents the chosen secret private key of each party.
Alice and Bob now mix the shared common color (yellow) with their respective secret color to produce a public color. Therefore, Alice will mix the yellow with her red color to produce a public color of orange. Bob will mix the yellow and the blue to produce a public color of green.
Alice sends her public color (orange) to Bob and Bob sends his public color (green) to Alice.
Alice and Bob each mix the color they received with their own, original secret color (Red for Alice and blue for Bob.). The result is a final brown color mixture that is identical to the partner’s final color mixture. The brown color represents the resulting shared secret key between Bob and Alice.
The security of DH is based on the fact that it uses very large numbers in its calculations. For example, a DH 1024-bit number is roughly equal to a decimal number of 309 digits. Considering that a billion is 10 decimal digits (1,000,000,000), one can easily imagine the complexity of working with not one, but multiple 309 digit decimal numbers.
Unfortunately, asymmetric key systems are extremely slow for any sort of bulk encryption. This is why it is common to encrypt the bulk of the traffic using a symmetric algorithm, such as 3DES or AES and use the DH algorithm to create keys that will be used by the encryption algorithm.
Ready to go! Keep visiting our networking course blog, give Like to our fanpage; and you will find more tools and concepts that will make you a networking professional.