Common Network Attacks
Summary
This topic describe common network attacks.. Start learning CCNA 200-301 for free right now!!
Table of Contents
Overview of Network Attacks
As you have learned, there are many types of malware that hackers can use. But these are not the only ways that they can attack a network, or even an organization.
When malware is delivered and installed, the payload can be used to cause a variety of network related attacks.
To mitigate attacks, it is useful to understand the types of attacks. By categorizing network attacks, it is possible to address types of attacks rather than individual attacks.
Networks are susceptible to the following types of attacks:
- Reconnaissance Attacks
- Access Attacks
- DoS Attacks
Video – Reconnaissance Attacks
Click Play in the figure to view a video about reconnaissance attacks.
Reconnaissance Attacks
Reconnaissance is information gathering. It is analogous to a thief surveying a neighborhood by going door-to-door pretending to sell something. What the thief is actually doing is looking for vulnerable homes to break into, such as unoccupied residences, residences with easy-to-open doors or windows, and those residences without security systems or security cameras.
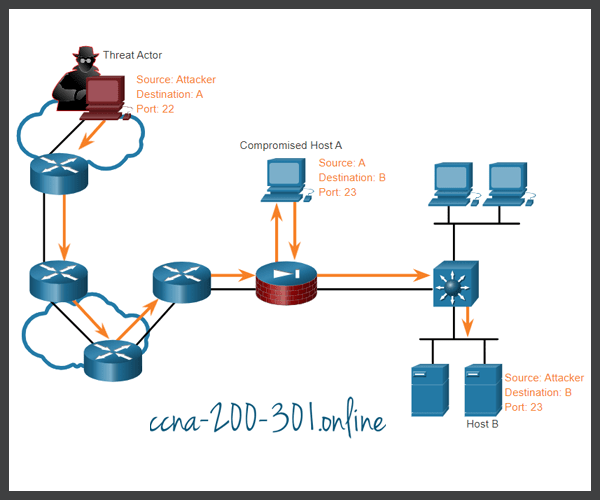
Threat actors use reconnaissance (or recon) attacks to do unauthorized discovery and mapping of systems, services, or vulnerabilities. Recon attacks precede access attacks or DoS attacks.
Some of the techniques used by malicious threat actors to conduct reconnaissance attacks are described in the table.
| Technique | Description |
|---|---|
| Perform an information query of a target | The threat actor is looking for initial information about a target. Various tools can be used, including the Google search, organizations website, whois, and more. |
| Initiate a ping sweep of the target network | The information query usually reveals the target’s network address. The threat actor can now initiate a ping sweep to determine which IP addresses are active. |
| Initiate a port scan of active IP addresses | This is used to determine which ports or services are available. Examples of port scanners include Nmap, SuperScan, Angry IP Scanner, and NetScanTools. |
| Run vulnerability scanners | This is to query the identified ports to determine the type and version of the application and operating system that is running on the host. Examples of tools include Nipper, Secuna PSI, Core Impact, Nessus v6, SAINT, and Open VAS. |
| Run exploitation tools | The threat actor now attempts to discover vulnerable services that can be exploited. A variety of vulnerability exploitation tools exist including Metasploit, Core Impact, Sqlmap, Social Engineer Toolkit, and Netsparker. |
Video – Access and Social Engineering Attacks
Click Play in the figure to view a video about access and social engineering attacks.
Access Attacks
Access attacks exploit known vulnerabilities in authentication services, FTP services, and web services. The purpose of these types of attacks is to gain entry to web accounts, confidential databases, and other sensitive information.
Threat actors use access attacks on network devices and computers to retrieve data, gain access, or to escalate access privileges to administrator status.
Password Attacks
In a password attack, the threat actor attempts to discover critical system passwords using various methods. Password attacks are very common and can be launched using a variety of password cracking tools.
Spoofing Attacks
In spoofing attacks, the threat actor device attempts to pose as another device by falsifying data. Common spoofing attacks include IP spoofing, MAC spoofing, and DHCP spoofing. These spoofing attacks will be discussed in more detail later in this module
Other Access attacks include:
- Trust exploitations
- Port redirections
- Man-in-the-middle attacks
- Buffer overflow attacks
Social Engineering Attacks
Social engineering is an access attack that attempts to manipulate individuals into performing actions or divulging confidential information. Some social engineering techniques are performed in-person while others may use the telephone or internet.
Social engineers often rely on people’s willingness to be helpful. They also prey on people’s weaknesses. For example, a threat actor could call an authorized employee with an urgent problem that requires immediate network access. The threat actor could appeal to the employee’s vanity, invoke authority using name-dropping techniques, or appeal to the employee’s greed.
Information about social engineering techniques is shown in the table.
| Social Engineering Attack | Description |
|---|---|
| Pretexting | A threat actor pretends to need personal or financial data to confirm the identity of the recipient. |
| Phishing | A threat actor sends fraudulent email which is disguised as being from a legitimate, trusted source to trick the recipient into installing malware on their device, or to share personal or financial information. |
| Spear phishing | A threat actor creates a targeted phishing attack tailored for a specific individual or organization. |
| Spam | Also known as junk mail, this is unsolicited email which often contains harmful links, malware, or deceptive content. |
| Something for Something | Sometimes called “Quid pro quo”, this is when a threat actor requests personal information from a party in exchange for something such as a gift. |
| Baiting | A threat actor leaves a malware infected flash drive in a public location. A victim finds the drive and unsuspectingly inserts it into their laptop, unintentionally installing malware. |
| Impersonation | This type of attack is where a threat actor pretends to be someone they are not to gain the trust of a victim. |
| Tailgating | This is where a threat actor quickly follows an authorized person into a secure location to gain access to a secure area. |
| Shoulder surfing | This is where a threat actor inconspicuously looks over someone’s shoulder to steal their passwords or other information. |
| Dumpster diving | This is where a threat actor rummages through trash bins to discover confidential documents. |
The Social Engineering Toolkit (SET) was designed to help white hat hackers and other network security professionals create social engineering attacks to test their own networks.
Enterprises must educate their users about the risks of social engineering, and develop strategies to validate identities over the phone, via email, or in person.
The figure shows recommended practices that should be followed by all users.
Recommended Social Engineering Protection Practices

Lab – Social Engineering
In this lab, you will research examples of social engineering and identify ways to recognize and prevent it.
Video – Denial of Service Attacks
Click Play in the figure to view a video about denial of service attacks.
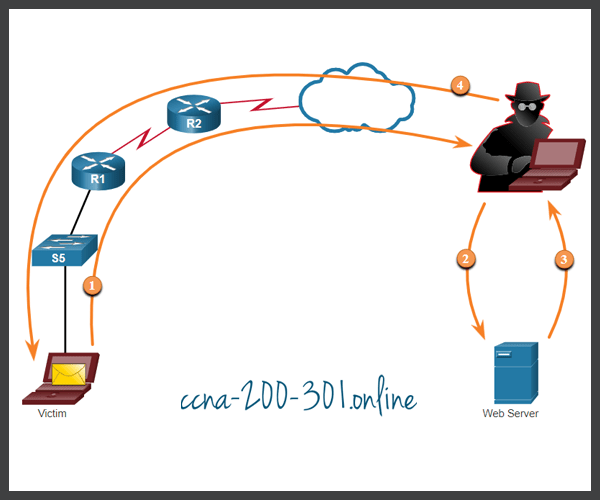
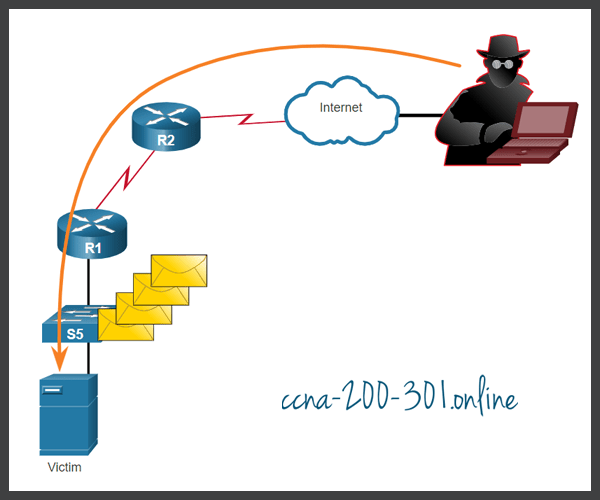
DoS and DDoS Attacks
A Denial of Service (DoS) attack creates some sort of interruption of network services to users, devices, or applications. There are two major types of DoS attacks:
- Overwhelming Quantity of Traffic – The threat actor sends an enormous quantity of data at a rate that the network, host, or application cannot handle. This causes transmission and response times to slow down. It can also crash a device or service.
- Maliciously Formatted Packets – The threat actor sends a maliciously formatted packet to a host or application and the receiver is unable to handle it. This causes the receiving device to run very slowly or crash.
Ready to go! Keep visiting our networking course blog, give Like to our fanpage; and you will find more tools and concepts that will make you a networking professional.