LAN Attacks
Summary
This topic explain how LAN attacks compromise LAN security. Start learning CCNA 200-301 for free right now!!
Video – VLAN and DHCP Attacks
This topic investigates the many different types of LAN attacks and their mitigation techniques. Like the previous topics, these attacks tend to be specific to switches and Layer 2.
Click Play in the figure to view a video about VLAN and DHCP attacks.
VLAN Hopping Attacks
A VLAN hopping attack enables traffic from one VLAN to be seen by another VLAN without the aid of a router. In a basic VLAN hopping attack, the threat actor configures a host to act like a switch to take advantage of the automatic trunking port feature enabled by default on most switch ports.
The threat actor configures the host to spoof 802.1Q signaling and Cisco-proprietary Dynamic Trunking Protocol (DTP) signaling to trunk with the connecting switch. If successful, the switch establishes a trunk link with the host, as shown in the figure. Now the threat actor can access all the VLANs on the switch. The threat actor can send and receive traffic on any VLAN, effectively hopping between VLANs.

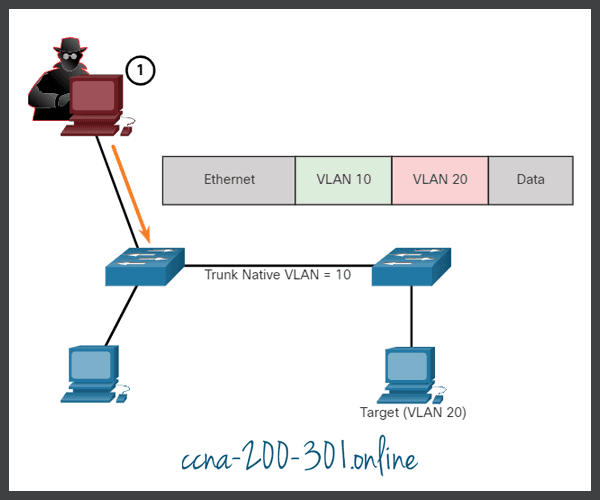
VLAN Double-Tagging Attack
A threat actor in specific situations could embed a hidden 802.1Q tag inside the frame that already has an 802.1Q tag. This tag allows the frame to go to a VLAN that the original 802.1Q tag did not specify.
Click each step for an example and explanation of a double-tagging attack.
A VLAN double-tagging attack is unidirectional and works only when the attacker is connected to a port residing in the same VLAN as the native VLAN of the trunk port. The idea is that double tagging allows the attacker to send data to hosts or servers on a VLAN that otherwise would be blocked by some type of access control configuration. Presumably the return traffic will also be permitted, thus giving the attacker the ability to communicate with devices on the normally blocked VLAN.
VLAN Attack Mitigation
VLAN hopping and VLAN double-tagging attacks can be prevented by implementing the following trunk security guidelines, as discussed in a previous module:
- Disable trunking on all access ports.
- Disable auto trunking on trunk links so that trunks must be manually enabled.
- Be sure that the native VLAN is only used for trunk links.
DHCP Messages
DHCP servers dynamically provide IP configuration information including IP address, subnet mask, default gateway, DNS servers, and more to clients. A review of the sequence of the DHCP message exchange between client and server is shown in the figure.

DHCP Attacks
Two types of DHCP attacks are DHCP starvation and DHCP spoofing. Both attacks are mitigated by implementing DHCP snooping.
DHCP Starvation Attack
The goal of the DHCP Starvation attack is to create a DoS for connecting clients. DHCP starvation attacks require an attack tool such as Gobbler.
Gobbler has the ability to look at the entire scope of leasable IP addresses and tries to lease them all. Specifically, it creates DHCP discovery messages with bogus MAC addresses.
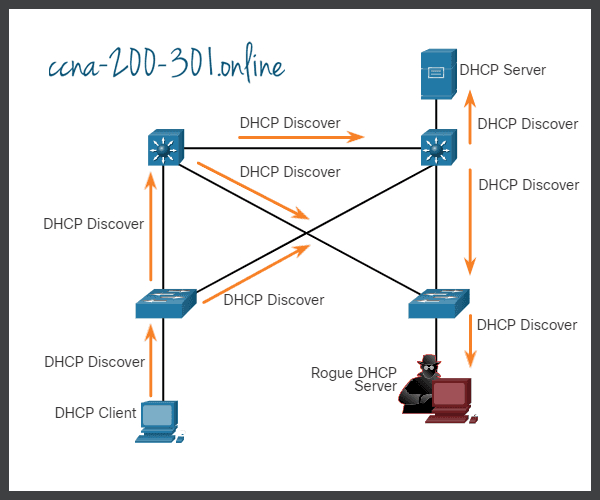
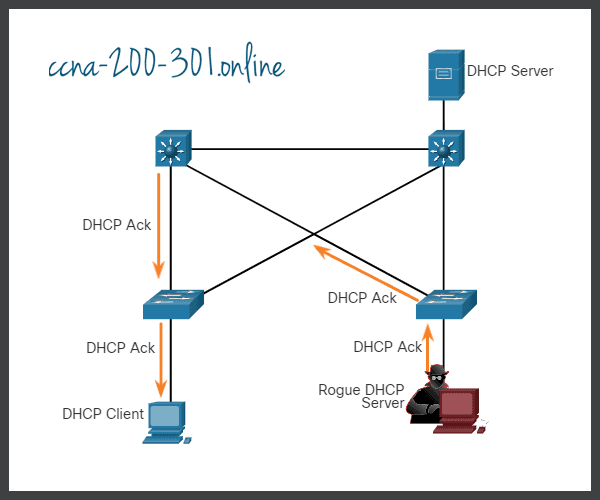
DHCP Spoofing Attack
A DHCP spoofing attack occurs when a rogue DHCP server is connected to the network and provides false IP configuration parameters to legitimate clients. A rogue server can provide a variety of misleading information:
- Wrong default gateway – The rogue server provides an invalid gateway or the IP address of its host to create a man-in-the-middle attack. This may go entirely undetected as the intruder intercepts the data flow through the network.
- Wrong DNS server – The rogue server provides an incorrect DNS server address pointing the user to a nefarious website.
- Wrong IP address – The rogue server provides an invalid IP address effectively creating a DoS attack on the DHCP client.
Click each step for an example and explanation of a DHCP spoofing attack.
Video – ARP Attacks, STP Attacks, and CDP Reconnaissance
Click Play in the figure to view a video about ARP Attacks, STP Attacks, and CDP Reconnaissance.
ARP Attacks
Recall that hosts broadcast ARP Requests to determine the MAC address of a host with a particular IP address. This is typically done to discover the MAC address of the default gateway. All hosts on the subnet receive and process the ARP Request. The host with the matching IP address in the ARP Request sends an ARP Reply.
According to the ARP RFC, a client is allowed to send an unsolicited ARP Reply called a “gratuitous ARP.” When a host sends a gratuitous ARP, other hosts on the subnet store the MAC address and IP address contained in the gratuitous ARP in their ARP tables.
The problem is that an attacker can send a gratuitous ARP message containing a spoofed MAC address to a switch, and the switch would update its MAC table accordingly. Therefore, any host can claim to be the owner of any IP and MAC address combination they choose. In a typical attack, a threat actor can send unsolicited ARP Replies to other hosts on the subnet with the MAC Address of the threat actor and the IP address of the default gateway.
There are many tools available on the internet to create ARP man-in-the-middle attacks including dsniff, Cain & Abel, ettercap, Yersinia, and others. IPv6 uses ICMPv6 Neighbor Discovery Protocol for Layer 2 address resolution. IPv6 includes strategies to mitigate Neighbor Advertisement spoofing, similar to the way IPv6 prevents a spoofed ARP Reply.
ARP spoofing and ARP poisoning are mitigated by implementing DAI.
Click each step for an example and explanation of ARP spoofing and ARP poisoning.
Address Spoofing Attack
IP addresses and MAC addresses can be spoofed for a variety of reasons. IP address spoofing is when a threat actor hijacks a valid IP address of another device on the subnet, or uses a random IP address. IP address spoofing is difficult to mitigate, especially when it is used inside a subnet in which the IP belongs.
MAC address spoofing attacks occur when the threat actors alter the MAC address of their host to match another known MAC address of a target host. The attacking host then sends a frame throughout the network with the newly-configured MAC address. When the switch receives the frame, it examines the source MAC address. The switch overwrites the current MAC table entry and assigns the MAC address to the new port, as shown in the figure. It then inadvertently forwards frames destined for the target host to the attacking host.
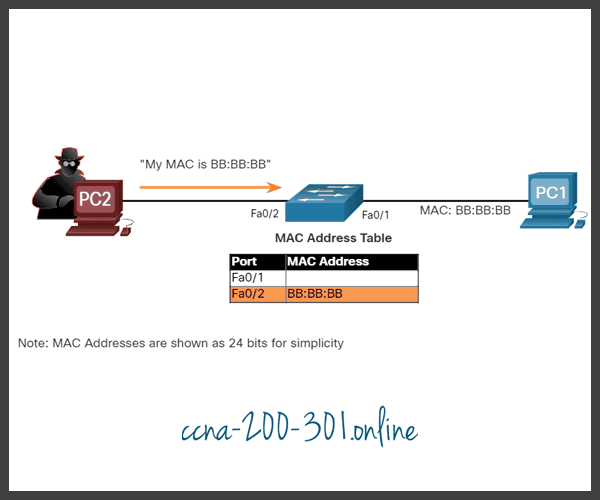
When the target host sends traffic, the switch will correct the error, realigning the MAC address to the original port. To stop the switch from returning the port assignment to its correct state, the threat actor can create a program or script that will constantly send frames to the switch so that the switch maintains the incorrect or spoofed information. There is no security mechanism at Layer 2 that allows a switch to verify the source of MAC addresses, which is what makes it so vulnerable to spoofing.
IP and MAC address spoofing can be mitigated by implementing IPSG.
STP Attack
Network attackers can manipulate the Spanning Tree Protocol (STP) to conduct an attack by spoofing the root bridge and changing the topology of a network. Attackers can make their hosts appear as root bridges; and therefore, capture all traffic for the immediate switched domain.
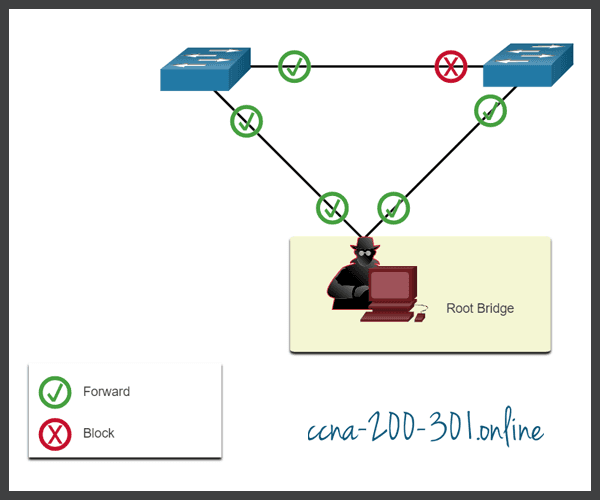
To conduct an STP manipulation attack, the attacking host broadcasts STP bridge protocol data units (BPDUs) containing configuration and topology changes that will force spanning-tree recalculations, as shown in the figure. The BPDUs sent by the attacking host announce a lower bridge priority in an attempt to be elected as the root bridge.

If successful, the attacking host becomes the root bridge, as shown in the figure, and can now capture a variety of frames that would otherwise not be accessible.
This STP attack is mitigated by implementing BPDU Guard on all access ports. BPDU Guard is discussed in more detail later in the course.
CDP Reconnaissance
The Cisco Discovery Protocol (CDP) is a proprietary Layer 2 link discovery protocol. It is enabled on all Cisco devices by default. CDP can automatically discover other CDP-enabled devices and help auto-configure their connection. Network administrators also use CDP to help configure and troubleshoot network devices.
CDP information is sent out CDP-enabled ports in periodic, unencrypted broadcasts. CDP information includes the IP address of the device, IOS software version, platform, capabilities, and the native VLAN. The device receiving the CDP message updates its CDP database.
CDP information is extremely useful in network troubleshooting. For example, CDP can be used to verify Layer 1 and 2 connectivity. If an administrator cannot ping a directly connected interface, but still receives CDP information, then the problem is most likely related to the Layer 3 configuration.
However, the information provided by CDP can also be used by a threat actor to discover network infrastructure vulnerabilities.
In the figure, a sample Wireshark capture displays the contents of a CDP packet. The attacker is able to identify the Cisco IOS software version used by the device. This allows the attacker to determine whether there were any security vulnerabilities specific to that particular version of IOS.

CDP broadcasts are sent unencrypted and unauthenticated. Therefore, an attacker could interfere with the network infrastructure by sending crafted CDP frames containing bogus device information to directly-connected Cisco devices.
To mitigate the exploitation of CDP, limit the use of CDP on devices or ports. For example, disable CDP on edge ports that connect to untrusted devices.
To disable CDP globally on a device, use the no cdp run global configuration mode command. To enable CDP globally, use the cdp run global configuration command.
To disable CDP on a port, use the no cdp enable interface configuration command. To enable CDP on a port, use the cdp enable interface configuration command.
Ready to go! Keep visiting our networking course blog, give Like to our fanpage; and you will find more tools and concepts that will make you a networking professional.